How does device validation work at login?
Did you know that to protect your Doppler account, we’ve added a security measure that allows us to validate whether you’re trying to log in from a device you don’t normally use?
Let’s find out what it’s all about in this article 🙂
What is this security measure about?
This functionality is intended to increase the security of your account to protect your Campaigns and Shipments. Occasionally, we add an additional layer of security for our clients’ accounts.
From now on, each user account will have an individual history of secure devices. This means that every time a user attempts to log in to Doppler, our application will detect the origin of that login and check if the device used has been previously approved as secure for that specific account.
What does this mean? Now, each account has its own history, which means that if a device is rejected by the account owner, it will only be rejected for that particular account. If the device has previously been approved as secure by the account owner, the next time you log in from that device a new confirmation will not be requested. The user will be able to access it without problems, just as she has done until now.
IMPORTANT:
If a device is rejected by the account owner, this information will be recorded in our database. From then on, even if the username and password are correct, access from that specific device will not be allowed.
This will ensure an additional level of security for all of our customers’ accounts.
How does security validation work on your account?
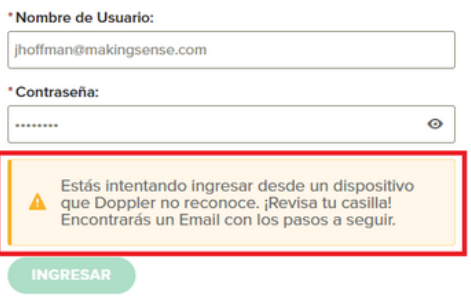
- When trying to log in and not being validated, you will see this message. From your Email account you can follow an instruction to confirm that it is you who is trying to access and continue with your access to Doppler.
- From your Email, you will see this message. There you will have 2 options: approve the device from which you are trying to access or reject it, if it is not you and protect your account.

Additionally, your account entry may be denied because the device from which you are attempting to enter was unknown. If you need to access it from that device that was rejected, what you can do is find the Email in your inbox and click the Approve button.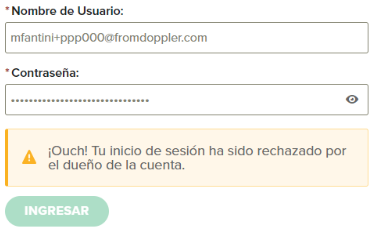
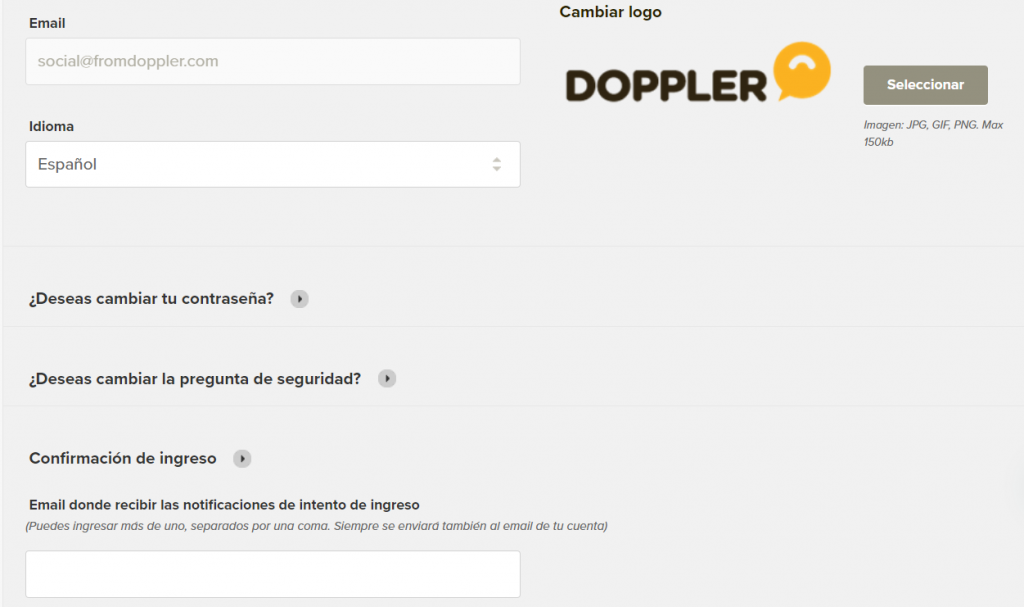
Also, in the Control Panel within the Account Information section you have the option to register one or more Emails to receive the login confirmation notification:
This way you will see this improvement from your account.
This means that you can not only approve or reject devices from the mailbox associated with your account, but you can also do so from other mailboxes. So that it is not just one person who verifies this instance, but there can be more than one and facilitate access to the tool in a more practical way.
So now you have all the information necessary to know how to access your account, with an improved level of security that will help protect your account.
If you have any questions or queries, you can write to us at [email protected]

 ES
ES EN
EN


Doppler informs you that the personal data that you provide to us when completing this form will be treated by Doppler LLC as responsible for this web.
Purpose: To allow you to make comments in our help center.
Legitimation: Consent of the applicant.
Recipients: Your data will be saved by Doppler and Digital Ocean as hosting company.
Additional information: In the Doppler Privacy Policy you’ll find additional information about the collection and use of your personal information by Doppler, including information on access, conservation, rectification, deletion, security, cross-border data transfers and other issues.